How to hack WordPress through plugins!
Word press is one of the most used blogging platforms, and word press core (word press without plugins) is pretty much secure already. As word press is a blogging platform we need additional plugins to extend its functionalities, there are many plugins available to even completely change your word press installation to an e-commerce site. But even the word press blogs needs a plugin to make good use of WordPress installation.
Most people use plugins:
- To fix their search engine optimization.
- Take WordPress Backups
- Track Visitors
- … and a lot more!
So how can you be sure that plugins you are installing are secure and do not open doors to vulnerabilities? Recently I was installing a visitors tracking plugin to my WordPress installation and I thought to check if its secure and did some testing on the plugin.
Plugin output not being sanitized
Plugin name is ‘Visitors Traffic Real Time Statistics‘, and it tracks visitors on the blog after you have installed and activated this plugin, open the following URL to open its dashboard:
http://yourdomain.com/wp-admin/admin.php?page=ahc_hits_counter_menu
The dashboard will look something like this:
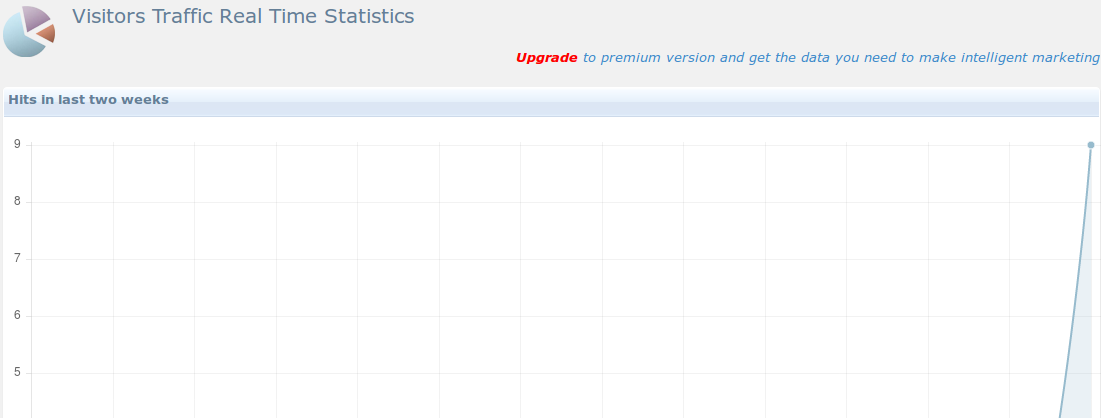
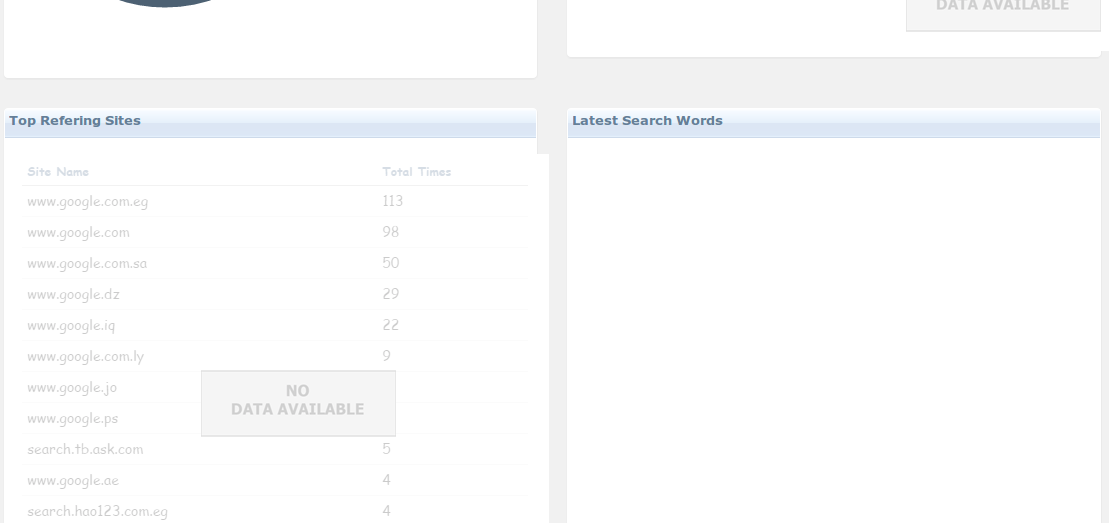
Our point of interest here will be “Top Referring site”, below this block websites who referred your site will appear. If any hacker that has access to the underlaying operating system by any means, he/she can easily execute malicious code on the visitors browsers of this site, by just inserting a simple record in the database.
If you look at your WordPress database, you can see that following tables are created by the plugin:
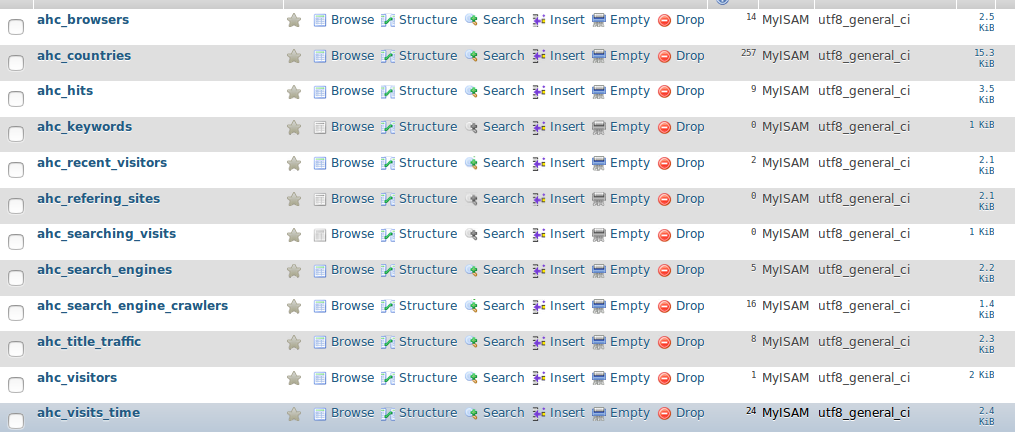
All tables prefixed with ahc are created by the plugins, now open the ‘ahc_referring_sites’ table and execute the following query:
INSERT INTO `ahc_refering_sites` (`rfr_id`, `rfr_site_name`, `rfr_visits`) VALUES ('1', '"><script>alert("xss")</script>', '1');
This query will insert a record in table, that will look something like this:
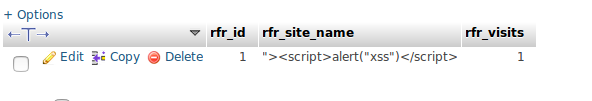
Now come back to WordPress and open this URL:
http://yourdomain.com/wp-admin/admin.php?page=ahc_hits_counter_menu , you will get JavaScript executed in the browser.
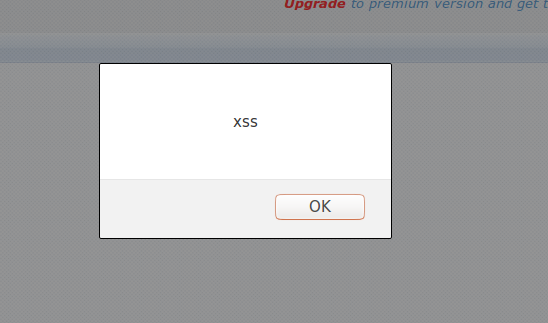
That means output is not being filtered properly and a website is vulnerable to XSS attack.
Plugin input not being sanitized
Normal HTTP request looks something like this:
GET /hello.html HTTP/1.1 User-Agent: Mozilla/4.0 (compatible; MSIE5.01; Windows NT) Host: www.cyberpersons.com Refer http://facebook.com Accept-Language: en-us Accept-Encoding: gzip, deflate Connection: Keep-Alive
Our point of interest here are two lines:
Refer http://facebook.com
or
User-Agent: Mozilla/4.0 (compatible; MSIE5.01; Windows NT)
You can use Burp proxy suite to modify your HTTP request and alter these header fields, and make them look like:
Refer: “><script>alert(“XSS”)</script>
User-Agent: “><script>alert(“XSS”)</script>
After altering these parameters of HTTP request, forward the request to the website, the script will use these fields data and store them in the database. If you see the records in ‘ahc_hits’ table, you might see a record something like this:
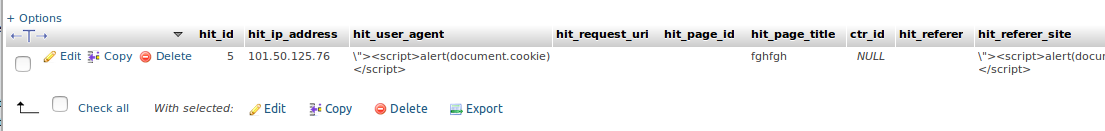
That means you are successfully able to inject JavaScript into the database.
Therefore you need to make sure that any third party plugins you are going to install on top of WordPress are secure and do not introduce vulnerabilities.
Wow! Very informative and very scary stuff.
I wish there was a website that listed all of the plugins that have shown vulnerabilities. Would probably be very difficult because of the thousands of plugins in the repository, but it would still be nice for those of us who don’t have the programming skills that you do.
George just make sure that all the plugins you have installed are upto date and their latest versions are installed.
[…] How to hack WordPress through plugins! | Linux Tutorials and Guides […]